 组件shell访问"/>
组件shell访问"/>
【Kerberos】开启了kerberos的ambari中组件shell访问
文章目录
- Ambari 与 Kerberos
- 访问hbase shell 示例
Ambari 与 Kerberos
在 Ambari 环境中,Kerberos 本身是作为 Ambari 的一个 Service 而存在。当用户通过 Ambari 的 Automated Kerberization 机制启用 Kerberos 认证的时候,Ambari 会为各个 Service 创建对应的 Principal 以及 Keytab 文件。在 Linux Redhat6(CentOS 6)上,Ambari 默认的会使用 Kerberos1.10.3 的版本,而在 Redhat7(CentOS 7)上,则默认使用 Kerberos1.13.2。因此,需要启用 Kerberos 认证的集群,需要注意 Kerberos 版本的兼容性问题。Ambari、Stack、Service 以及 KDC 的关系大致如下图所示:
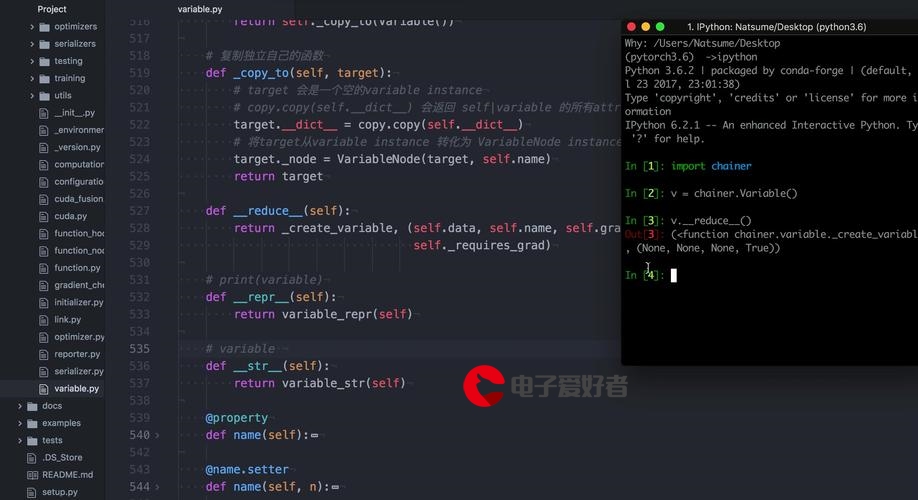
我们再看一下开启了kerberos的一些配置信息
从配置中我们知道keytabs信息存储在/etc/security/keytabs目录下:
[root@10.211.55.60 keytabs]# ll /etc/security/keytabs
total 116
-r-------- 1 root root 368 Mar 2 19:04 ambari.server.keytab
-r-------- 1 ams hadoop 383 Mar 2 19:04 ams.collector.keytab
-r-------- 1 ams hadoop 383 Mar 2 19:04 ams-hbase.master.keytab
-r-------- 1 ams hadoop 383 Mar 2 19:04 ams-hbase.regionserver.keytab
-r-------- 1 ams hadoop 373 Mar 2 19:04 ams-monitor.keytab
-r-------- 1 ams hadoop 368 Mar 2 19:04 ams-zk.service.keytab
-r-------- 1 hdfs hadoop 353 Mar 2 19:04 dn.service.keytab
-r--r----- 1 hbase hadoop 328 Mar 2 19:04 hbase.headless.keytab
-r-------- 1 hbase hadoop 368 Mar 2 19:04 hbase.service.keytab
-r-------- 1 hdfs hadoop 323 Mar 2 19:04 hdfs.headless.keytab
-r--r----- 1 yarn hadoop 363 Mar 2 19:04 hive.llap.task.keytab
-r--r----- 1 hive hadoop 363 Mar 2 19:04 hive.service.keytab
-r-------- 1 mapred hadoop 358 Mar 2 19:04 jhs.service.keytab
-r-----r-- 1 root root 383 Aug 14 2019 kafka.service.keytab
-rw-r----- 1 ambari-qa hadoop 338 Mar 2 19:04 kerberos.service_check.022920.keytab
-rw-r----- 1 ambari-qa hadoop 338 Mar 2 19:04 kerberos.service_check.030220.keytab
-r-------- 1 yarn hadoop 353 Mar 2 19:04 nm.service.keytab
-r-------- 1 hdfs hadoop 353 Mar 2 19:04 nn.service.keytab
-r-------- 1 ranger root 398 Mar 2 19:04 rangeradmin.service.keytab
-r-------- 1 ranger root 403 Mar 2 19:04 rangerlookup.service.keytab
-r-------- 1 ranger root 413 Mar 2 19:04 rangerusersync.service.keytab
-r-------- 1 yarn hadoop 353 Mar 2 19:04 rm.service.keytab
-r--r----- 1 ambari-qa hadoop 348 Mar 2 19:04 smokeuser.headless.keytab
-r--r----- 1 root hadoop 363 Mar 2 19:04 spnego.service.keytab
-r-------- 1 yarn-ats hadoop 343 Mar 2 19:04 yarn-ats.hbase-client.headless.keytab
-r-------- 1 yarn-ats hadoop 413 Mar 2 19:04 yarn-ats.hbase-master.service.keytab
-r-------- 1 yarn-ats hadoop 413 Mar 2 19:04 yarn-ats.hbase-regionserver.service.keytab
-r-------- 1 yarn hadoop 363 Mar 2 19:04 yarn.service.keytab
-r-------- 1 zookeeper hadoop 388 Mar 2 19:04 zk.service.keytab
以及为我们生成的一些principals,我们可以listprincs看一下:
kadmin.local: listprincs
HTTP/host-10-211-55-60@HONEY.COM
K/M@HONEY.COM
admin/admin@HONEY.COM
ambari-qa-testcluster@HONEY.COM
ambari-server-testcluster@HONEY.COM
amshbase/host-10-211-55-60@HONEY.COM
amsmon/host-10-211-55-60@HONEY.COM
amszk/host-10-211-55-60@HONEY.COM
dn/host-10-211-55-60@HONEY.COM
hbase-testcluster@HONEY.COM
hbase/host-10-211-55-60@HONEY.COM
hdfs-testcluster@HONEY.COM
hive/host-10-211-55-60@HONEY.COM
jhs/host-10-211-55-60@HONEY.COM
kadmin/10.1.236.60@HONEY.COM
kadmin/admin@HONEY.COM
kadmin/changepw@HONEY.COM
kadmin/host-10-211-55-60@HONEY.COM
kiprop/host-10-211-55-60@HONEY.COM
krbtgt/HONEY.COM@HONEY.COM
testcluster-022920@JIAZZ.COM
testcluster-030220@JIAZZ.COM
nm/host-10-211-55-60@HONEY.COM
nn/host-10-211-55-60@HONEY.COM
rangeradmin/host-10-211-55-60@HONEY.COM
rangerlookup/host-10-211-55-60@HONEY.COM
rangerusersync/host-10-211-55-60@HONEY.COM
rm/host-10-211-55-60@HONEY.COM
yarn-ats-hbase/host-10-211-55-60@HONEY.COM
yarn-ats-testcluster@HONEY.COM
yarn/host-10-211-55-60@HONEY.COM
zookeeper/host-10-211-55-60@HONEY.COM
访问hbase shell 示例
我们像往常一样访问hbase shell,我们可以进入shell,但是我们却没有权限做任何操作ERROR: No valid credentials provided (Mechanism level: Failed to find any Kerberos tgt)
[root@host-10-211-55-60 keytabs]# hbase shell
hbase(main):001:0> list
TABLE ERROR: No valid credentials provided (Mechanism level: Failed to find any Kerberos tgt)For usage try 'help "list"'Took 8.7254 seconds
hbase(main):002:0> create 'hb_test','base_info'ERROR: No valid credentials provided (Mechanism level: Failed to find any Kerberos tgt)For usage try 'help "create"'Took 8.1969 seconds
所以开启了kerberos后的服务,就要使用keytab证明我们这个客户端有权限
[root@host-10-211-55-60 keytabs]# kinit -kt hbase.headless.keytab hbase-testcluster@HONEY.COM
[root@host-10-211-55-60 keytabs]# klist
Ticket cache: FILE:/tmp/krb5cc_0
Default principal: hbase-testcluster@HONEY.COMValid starting Expires Service principal
03/03/2020 10:36:24 03/04/2020 10:36:24 krbtgt/HONEY.COM@HONEY.COM
[root@host-10-211-55-60 keytabs]# hbase shell
hbase(main):002:0> create 'hb_test','base_info'
Created table hb_test
Took 4.5764 seconds
=> Hbase::Table - hb_test
hbase(main):003:0> list
TABLE
hb_test
1 row(s)
Took 0.0303 seconds
=> ["hb_test"]比如我要继续访问hdfs,当前hbase的principle就有权限访问hdfs,不需要切换
[hdfs@host-10-211-55-60 honey]$ hdfs dfs -put /home/hdfs/word.txt /dataDir/ww.txt
[hdfs@host-10-211-55-60 honey]$ kdestroy
[hdfs@host-10-211-55-60 honey]$ hdfs dfs -put /home/hdfs/word.txt /dataDir/wx.txt
20/03/03 11:14:33 WARN ipc.Client: Exception encountered while connecting to the server : org.apache.hadoop.security.AccessControlException: Client cannot authenticate via:[TOKEN, KERBEROS]
put: DestHost:destPort host-10-211-55-60:8020 , LocalHost:localPort host-10-211-55-60/10.211.55.60:0. Failed on local exception: java.io.IOException: org.apache.hadoop.security.AccessControlException: Client cannot authenticate via:[TOKEN, KERBEROS]
这样不同组件不同principal来回切换,当然很麻烦,所以直接kinit admin/admin@REALM就好了。
参考链接
.html
更多推荐
【Kerberos】开启了kerberos的ambari中组件shell访问












发布评论