 防火墙"/>
防火墙"/>
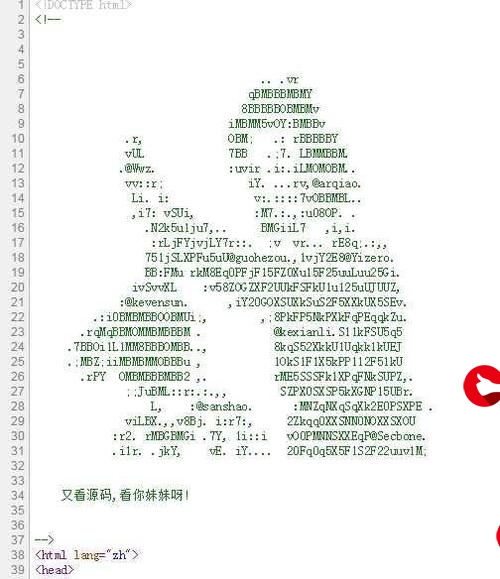
open bsd pf 软件防火墙
通过BSD系统,配置PF软件,提供防火墙服务
安装BSD操作系统,配置双网卡路由,启动PF,配置PF防火墙核心配置,可用文件来定义需要使用防火墙的用户组
# vi /etc/pf.conf
########################################
#### pf configuration for XXX GROUP
#### Version 1.0
#### Build by jekc
#### 2017-03-18
########################################
########################################
#### Required order:
#### options, queueing, translation and filtering.
########################################
########## Tables ##############################
table <admin_ext> persist file "/etc/admin_ext"
table <led_ext> persist file "/etc/led_ext"
table <com_ext> persist file "/etc/com_ext"
#################### Macros ####################
#### Interfaces ####
int_if = "em0"
ext_if = "em1"
#### Hosts ####
Admin_Station = " 172.20.0.8 "
jekc = " 172.20.0.8 "
Win_XP = " 172.20.0.80 "
Win_08 = " 172.20.0.10 "
# ftp_srv = "172.20.0.150"
# pd_srv = " 172.20.0.151 "
com_ext = " <com_ext> "
# wifi_ext = " 172.22.0.0/16 "
oa_srv = " 172.20.0.56 "
server_srv = " 172.20.0.50 "
k301_srv = " 172.20.0.51 "
k303_srv = " 172.20.0.134"
oasrv01_srv =" 172.20.0.59"
#### Ports ####
WWW_Server_Ports = "{ www }"
ICMP_types = " echoreq "
Torrent_Port = " 32058 "
emule_Port = " 32968 "
mysqld_SSH_Port = " 8022 "
mysql_Port = " 3306 "
oa_msn ="1188"
oa_web="8000"
oa_port="{1188,8000}"
server_sql="56433"
server_telnet="4587"
server_port="{56433,4587}"
k301_ld_01="20080"
k304_rdp ="3390"
k301_ld_02="20081"
k301_ld_03="20082"
k301_ld_04="20083"
k301_ld_05="20084"
k301_ld_06="20085"
k301_ld_port="{20080:20085}"
k301_ry_01="81"
k301_ry_02="82"
k301_ry_port=" { 81,82 } "
k301_web_port = " 8688 "
k303_port = " { 83,3389 } "
k303_ry_port = " 83 "
k303_rdp_port = " 3389 "
oasrv01_port = " { 89,8899,33389 } "
#### Lists and Tables ####
rfc1918 = "{ 192.168.0.0/16, 172.16.0.0/12, 10.0.0.0/8, 127.0.0.0/8, 169.254.0.0/16, 192.0.2.0/24, 0.0.0.0/8, 240.0.0.0/4 }"
#### Queues, States and Types ####
#### Stateful Tracking Options ####
#################### Options ####################
#### Misc Options ####
set debug urgent
set reassemble yes
# set require-order yes
set block-policy drop
set loginterface $ext_if
set state-policy if-bound
set skip on lo
#### Timeout Options ####
#################### Queueing ####################
#################### Translation and Filtering ####################
#### Blocking spoofed packets ####
antispoof log quick for lo
#### Block to/from illegal sources/destinations ####
block quick inet6
block in quick on $ext_if inet from any to 255.255.255.255
block in quick on $ext_if inet from urpf-failed to any
block in quick on $ext_if inet from $rfc1918 to any
#### Block all in/out on all interfaces by default and log ####
block log on $ext_if
# block return log on $int_if
block log on $ext_if inet proto icmp all
block return-rst in log on $ext_if proto tcp from any to any flags S/SA
block return-icmp(net-unr) in log on $ext_if proto udp from any to any
#### NAT with outgoing source port randomization ####
match out log on $ext_if inet from { $com_ext $Admin_Station } to any received-on $int_if nat-to $ext_if:0 port 4096:65535
# rdr on $int_if inet proto tcp from $int_if to any port 80 -> 127.0.0.1 port 8080
#### Packet normalization ( "scrubbing" ) ####
#### Externet Inbound ####
pass in log on $ext_if inet proto tcp from any to $ext_if port ssh
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port ntp
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port domain
# pass in log on $ext_if inet proto icmp all icmp-type $ICMP_types
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $oa_port rdr-to $oa_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $server_port rdr-to $server_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k301_ld_port rdr-to $k301_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k301_web_port rdr-to $k301_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k301_ry_port rdr-to $k301_srv
# pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k303_ry_port rdr-to $k303_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k303_port rdr-to $k303_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port $k304_rdp rdr-to $k303_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port {89,8899,33899} rdr-to $oasrv01_srv
pass in log on $ext_if inet proto { tcp udp } from any to $ext_if port {5208} rdr-to $jekc
#### Internal Outbound ####
pass out log on $int_if inet
#### Internal Inbound ####
pass in log on $int_if inet proto { tcp udp } from any to $int_if port ntp
pass in log on $int_if inet proto tcp from $Admin_Station to $int_if port ssh
pass in log on $int_if inet proto { tcp udp } from { $com_ext } to any
# pass in log on $int_if inet proto { tcp udp } from { $com_ext } to $int_if port icmp
#### Externet Outbound ####
pass out log on $ext_if inet from $ext_if to any
########################################
#### The EnD
########################################
vi /etc/rc.local
# $OpenBSD: rc.local,v 1.44 2011/04/22 06:08:14 ajacoutot Exp $
# Site-specific startup actions, daemons, and other things which
# can be done AFTER your system goes into securemode. For actions
# which should be done BEFORE your system has gone into securemode
# please see /etc/rc.securelevel.
route add -net 172.20.0.0 -netmask 255.255.0.0 172.20.1.2
route add -net 172.21.0.0 -netmask 255.255.254.0 172.20.7.1
route add default 6.X.X.X
vi /etc/admin_ext
172.20.0.0/16
~
更多推荐
open bsd pf 软件防火墙












发布评论